Data Privacy in Cloud-Native Telematics Systems
Guidance for UK fleet operators on GDPR-aligned cloud-native telematics: consent, minimisation, encryption, RBAC and secure APIs.

Fleet operators in the UK face a dual challenge: leveraging cloud-native telematics solutions for efficiency while ensuring compliance with GDPR and UK data laws. These systems collect sensitive data - like GPS locations and driver behaviours - which are classified as personal under GDPR. Mishandling such data can lead to heavy penalties, reputational damage, and legal consequences.
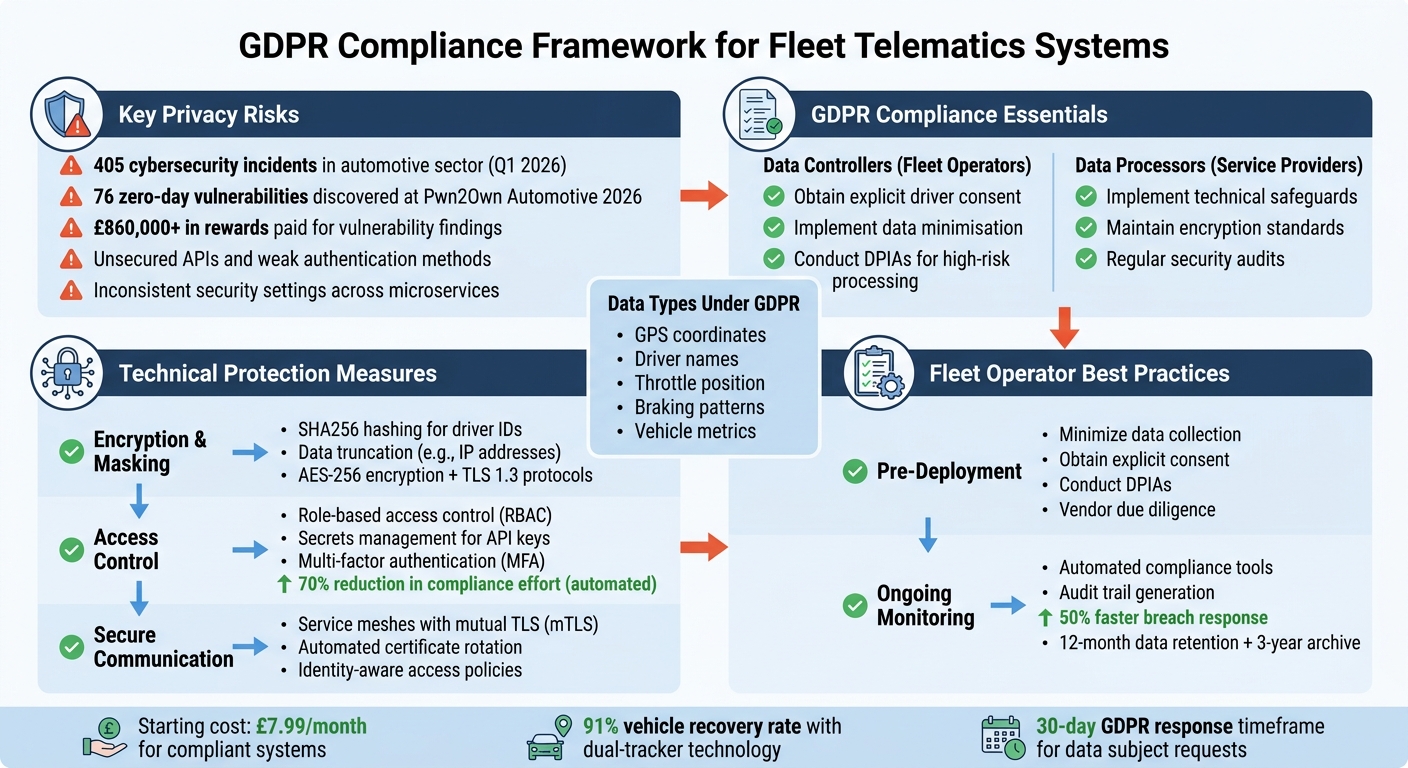
Key points to address include:
- Privacy risks: Unsecured APIs, poor encryption, and inconsistent security settings leave systems vulnerable to cyber threats.
- GDPR compliance: Operators must secure explicit consent from drivers, minimise data collection, and adopt strong safeguards like encryption and secure protocols.
- Technical measures: Encryption, role-based access control, and service meshes help secure data and prevent breaches.
- Driver trust: Transparency in data usage and informed consent are critical to maintaining compliance and trust.
GDPR Compliance Framework for Fleet Telematics Systems
Cloud-Native Telematics Systems and Privacy Risks
What Defines a Cloud-Native Telematics System?
Cloud-native telematics systems rely on microservices, APIs, and cloud platforms to link vehicle TCUs (Telematics Control Units) with backend systems. Unlike traditional systems that store data locally, these platforms transmit real-time data - such as location and vehicle metrics - to remote servers for analysis and processing. This setup allows fleet operators to scale operations efficiently, integrate with third-party analytics tools, and access data from virtually anywhere with an internet connection.
Today’s telematics systems go beyond basic data transmission. Many now incorporate AI-driven features to predict maintenance needs, optimise routes, and even influence vehicle behaviour directly. As vehicles transition into Software-Defined Vehicles (SDVs), telematics becomes a core element of fleet management. But while these advancements boost operational efficiency, they also open the door to greater security risks.
The distributed nature of these systems, while advantageous, introduces notable privacy concerns.
Main Data Privacy Risks in Telematics Systems
The decentralised framework of cloud-native systems creates opportunities for vulnerabilities. Unsecured APIs and backend services are particularly risky, as they can expose sensitive vehicle data. For instance, VicOne reported 405 cybersecurity incidents in the automotive sector during Q1 2026, with incidents involving EV charging infrastructure tripling in number. At the Pwn2Own Automotive 2026 event, researchers uncovered 76 zero-day vulnerabilities, earning over £860,000 in rewards for their findings.
Weak authentication methods further compound these risks. Some systems still use poor practices, like transmitting cleartext passwords in URI parameters or employing outdated encryption methods for logins. Such flaws can allow attackers to take over entire fleet management platforms. Technology writer Josh Lee aptly notes:
If you're not careful, your app could get exposed to attacks or miss key regulations. That's a headache nobody wants.
Another challenge lies in maintaining consistent security settings across various microservices and industries. Disparities in these settings can lead to compliance gaps, creating additional opportunities for breaches.
Under GDPR, the scope of personal data is broad. Beyond obvious identifiers like GPS coordinates or driver names, data such as throttle position or braking patterns can also be classified as personal when used to trigger specific alerts or feedback. This complexity is further exacerbated by the interconnected nature of telematics ecosystems. A single security lapse - whether from a hardware supplier or an analytics provider - can compromise the entire system. As TruckerCloud highlights:
If the data isn't safe, neither are the insights, and the risks ripple far beyond the balance sheet.
These risks underscore the importance of robust technical safeguards. For fleet operators, ensuring GDPR compliance means securing every layer of their telematics infrastructure. From APIs to third-party integrations, a comprehensive approach is essential to mitigate vulnerabilities and protect sensitive data.
sbb-itb-499a7f0
Connected Cars Explained: Telematics, Privacy, and the Future of Mobility
GDPR and UK Data Privacy Compliance Requirements
To address potential risks effectively, adhering to GDPR and UK-specific data protection laws is crucial.
GDPR Roles and Responsibilities
Fleet operators need to understand their role under GDPR. Acting as data controllers, they decide how and why telematics data is processed. This means they must obtain explicit consent from drivers before collecting any data.
Telematics service providers, on the other hand, function as data processors, managing data on behalf of fleet operators. They are responsible for implementing strong technical and organisational safeguards to protect the data. Any security breach by these third-party vendors directly impacts the fleet operator's compliance status.
GDPR applies to both direct identifiers (like GPS coordinates or driver names) and indirect data. Compliance requires fleet operators to follow the data minimisation principle, meaning they should only collect and track data that is absolutely necessary for operational purposes.
Under Article 32, organisations are required to adopt measures such as:
- Encryption of sensitive data.
- Secure transmission protocols.
- Regular audits.
- Data Protection Impact Assessments (DPIAs) for high-risk data processing activities.
Understanding these responsibilities is key to navigating the additional requirements specific to the UK.
UK-Specific Compliance Rules
UK businesses managing van tracker systems must also account for additional obligations. Following Brexit, the UK GDPR, alongside the Data Protection Act 2018, governs this area, introducing unique provisions. Fleet operators need to ensure their data practices are transparent, serve a legitimate purpose, and are based on informed consent from drivers.
For international data transfers, UK businesses must use approved mechanisms like Standard Contractual Clauses (SCCs) to comply with changing regulations. Additionally, the European Court of Human Rights underscores the need for workplace privacy. This means fleet monitoring must be justified, proportionate, and respectful of employee rights. Drivers must be informed about what data is collected, how it is used, and must provide explicit consent. Failing to do so could result in severe penalties.
It’s also essential for fleet operators to establish clear data protection agreements with third-party vendors. Conducting regular audits of hardware, software, and analytics providers ensures ongoing compliance with GDPR standards. As TruckerCloud highlights:
Data is both an asset and a liability. A breach doesn't just create operational headaches. It can mean financial penalties, legal consequences, and lasting reputational damage.
These regulatory guidelines lay the groundwork for the technical solutions and best practices to follow.
Technical Solutions for Data Privacy Protection
Protecting telematics data goes beyond just meeting regulatory requirements. It demands a solid set of technical measures to ensure data security throughout its lifecycle. By combining encryption, access controls, and secure communication protocols, fleet operators can significantly lower the risk of data breaches while keeping operations running smoothly with white-label van tracking solutions.
Data Encryption and Masking Methods
When dealing with sensitive telematics data, protection starts with limiting what data is collected to only what is absolutely necessary for operations.
For essential data, techniques like hashing algorithms (e.g., SHA256) can pseudonymise identifiers such as driver IDs or email addresses. However, hashing has its limits, especially when the input data is small or predictable. In such cases, data truncation can be a better option. For example, truncating IPv4 addresses (192.168.1.45 becomes 192.168.1.0) helps anonymise location details while still allowing for network analysis.
Another effective method is using regular expressions to mask sensitive data during transmission. For instance, fleet operators can configure transform processors to replace the last octet of IP addresses with .0, anonymising the data before it reaches storage systems. Similarly, redaction processors can remove any attributes not on a pre-approved list, preventing accidental exposure of personally identifiable information from system updates.
In cloud-native setups using OpenTelemetry, the Collector acts as a central hub where these techniques can be applied. By using attribute filters, redaction, and transform processors, sensitive data is safeguarded right at the start of the pipeline, reducing the risk of exposure.
Once data is encrypted and masked, the next step is controlling who has access to it.
Role-Based Access Control and Secrets Management
Even encrypted data can be at risk if it falls into the wrong hands. This is where role-based access control (RBAC) comes in, ensuring only authorised personnel can access or modify sensitive data and system settings.
In telematics systems, such as van tracking for rental and leasing companies, RBAC allows for granular control, letting organisations specify who can access certain types of data, whether it’s GPS history, driver behaviour analytics, or operational details. This level of control is crucial because telematics data often includes real-time tracking and behavioural insights, which could be misused for fraud or theft if not properly managed.
RBAC works best when paired with secrets management tools. These tools secure API keys, passwords, and tokens, ensuring they don’t fall into unauthorised hands. Automating compliance processes, including access controls and monitoring, can reduce operational effort related to compliance by up to 70%. Moreover, structured data management and controlled access can streamline breach investigations, cutting response times by 50%.
To strengthen security further, fleet operators should avoid broad access categories and instead implement specific permissions that define exactly what users can do with telematics data. Regular audits - both automated and manual - are essential for spotting misconfigurations or issues that software might overlook.
In addition to access controls, securing communication between services is another critical component.
Service Meshes for Secure Communication
In modern cloud-native telematics systems, where microservices are the backbone, securing communication between these services is a priority. This is where service meshes come into play, providing a dedicated layer for managing secure service-to-service communication.
One of the key features of service meshes is mutual TLS (mTLS). Unlike standard TLS (used in HTTPS), where only the client verifies the server’s certificate, mTLS requires both the client and server to authenticate each other. This ensures a higher level of trust and security.
Service meshes also automate the management of certificates and keys, including their issuance and rotation via a private Certificate Authority. This automation is crucial for maintaining security in dynamic microservice environments.
Another advantage of service meshes is the ability to define security policies declaratively. These policies can enforce identity-aware access control based on service identities or Kubernetes namespaces rather than relying on IP addresses, which can frequently change in containerised environments. This identity-based approach is far more reliable than traditional IP-based segmentation.
Additionally, service meshes provide detailed access logging, capturing the mTLS identity of the client. This ensures better tracking and auditing of sensitive data access, even when workloads are ephemeral or spread across multiple clusters.
Data Privacy Strategies for Fleet Operators
Protecting telematics data requires a well-thought-out approach that considers privacy from the initial planning phase through to ongoing operations.
Privacy Best Practices Before Deployment
Before activating telematics systems, fleet operators should put strong privacy measures in place. Start with data minimisation - ask whether continuous GPS tracking is truly necessary, or if periodic location updates will meet operational needs. It’s also vital to obtain explicit driver consent, ensuring drivers are fully aware of what data is being collected, why, and how it will be used.
For high-risk data processing, conduct Data Protection Impact Assessments (DPIAs). These assessments, required under GDPR’s Article 32, help identify risks early and allow for proactive solutions. The goal is to implement technical and organisational safeguards that match the level of risk involved.
Thorough vendor due diligence is another key step. Even if third-party vendors are involved, the responsibility for compliance remains with the fleet operator. Regular audits, along with clear data protection agreements, ensure vendors adhere to GDPR’s security standards. For transferring data internationally, stick to approved frameworks like Standard Contractual Clauses to stay compliant.
Once these foundational measures are in place, the focus shifts to consistent monitoring to ensure data privacy remains intact.
Monitoring and Compliance Tools
Staying compliant isn’t a one-time task - it requires ongoing attention. Automated monitoring tools can track who accesses data and how it’s used, generating detailed audit trails that simplify compliance reporting. Adding multi-factor authentication (MFA) and identity management systems ensures users only have access to what they absolutely need.
For cloud-stored data, automated services can locate and secure sensitive information, while encryption key management systems safeguard data at rest. It’s also important to avoid embedding sensitive details in metadata or free-text fields, which could inadvertently expose confidential information.
How GRS Fleet Telematics Protects Your Data
GRS Fleet Telematics takes data security seriously, employing end-to-end encryption across its entire tracking system. Every piece of information - whether it's location data, driver behaviour metrics, or vehicle diagnostics - is protected using AES-256 encryption paired with TLS 1.3 protocols, ensuring compliance with GDPR Article 32. This means your data remains encrypted both during transmission and while stored in cloud servers. Even internal staff cannot access raw tracking data unless explicitly authorised.
The system also includes additional privacy safeguards. For example, its dual-tracker technology not only contributes to an impressive 91% vehicle recovery rate but also strengthens data security. Each tracker independently records and encrypts data, creating a backup system that ensures privacy even if one tracker fails or is compromised. If discrepancies arise between the two data streams, automated security alerts are triggered immediately, maintaining compliance with UK data protection laws.
Role-based access control further limits who can view specific data. Fleet managers, for instance, can access aggregated vehicle performance data, while drivers see only details related to their own vehicle, such as maintenance alerts. Administrative staff are restricted to anonymised usage metrics, avoiding exposure to sensitive real-time location data. Every access request is logged, detailing who accessed what, when, and from which device. Security is bolstered with multi-factor authentication for administrative users and authentication tokens that rotate every 90 days.
For individuals exercising their data subject rights, GRS Fleet Telematics has automated systems in place to handle requests within GDPR's 30-day response timeframe. Detailed tracking data is retained for 12 months to meet compliance and insurance requirements, after which it is archived for three years before undergoing secure deletion using cryptographic erasure. A 24/7 monitoring centre also keeps an eye out for suspicious activity. Machine learning algorithms establish normal usage patterns and flag anomalies, such as unusual download activity or access from unexpected locations, ensuring proactive threat detection.
These robust security measures are backed by industry-leading certifications. The company holds ISO/IEC 27001 certification and undergoes annual SOC 2 Type II audits conducted by Big Four firms. UK customers benefit from domestic data storage options, while international transfers are secured using Standard Contractual Clauses, enhanced by additional encryption and pseudonymisation. All of this is included in the standard pricing, starting at just £7.99 per month, with no hidden fees for compliance features.
Conclusion
Cloud-native telematics data, such as vehicle location, driver behaviour, and maintenance records, falls under personal data according to GDPR. Even indirect information, like anonymised throttle position datasets used to influence decisions, requires careful handling and protection.
Fleet operators bear full responsibility for compliance, even when working with third-party vendors. Striking a balance between operational needs and privacy requires well-defined policies and strong safeguards.
Key measures include securing explicit driver consent, limiting data collection to what’s necessary, performing DPIAs for high-risk activities, and implementing encryption alongside secure transfer protocols. For cross-border data transfers, Standard Contractual Clauses ensure adherence to GDPR requirements. When combined with technical safeguards, these practices provide a comprehensive approach to data privacy.
Cloud migration offers an opportunity to strengthen security through compliant systems and advanced protections. By aligning legal requirements with cutting-edge technical solutions, fleet operators can protect driver privacy, maintain operational efficiency, and build trust through a secure, compliant approach.
FAQs
Do drivers always need to give explicit consent for telematics tracking?
Drivers aren't always required to give explicit consent for telematics tracking, as long as the data collection adheres to legal standards like GDPR and UK data protection laws. These regulations ensure that businesses provide clear information about how data is collected and processed, promoting transparency and compliance.
What telematics data counts as personal data under UK GDPR?
Under UK GDPR, telematics data is classified as personal data if it can directly or indirectly identify an individual. This includes details like GPS location, driver behaviour, and other personal identifiers. Businesses that collect or process this type of data must manage it carefully to remain compliant with privacy regulations. Mismanagement could lead to breaches and potential penalties, so handling this data responsibly is essential.
How can we secure microservices and APIs in a cloud-native telematics platform?
To protect microservices and APIs within a cloud-native telematics platform, prioritise encryption - use methods like AES-GCM for securing data at rest and TLS 1.2 or higher for safeguarding data in transit. Strengthen access controls by incorporating multi-factor authentication (MFA) and role-based access control (RBAC) to ensure only authorised users have access.
Keep security robust by conducting regular API audits, actively monitoring for potential threats, and staying compliant with UK GDPR and the Data Protection Act 2018. This includes obtaining user consent, limiting data collection to what's strictly necessary, and performing Data Protection Impact Assessments (DPIAs) to identify and mitigate privacy risks.




