Best Practices for OTA Telematics Updates
Secure, reliable OTA telematics updates: encryption, staged rollouts, A/B fail-safes, delta updates and real-time monitoring.

Over-the-air (OTA) telematics updates allow vehicles to receive software or firmware updates wirelessly, saving time and costs compared to physical updates or recalls. For fleet operators, this approach is essential to manage large vehicle fleets efficiently with van tracking solutions. However, OTA updates come with challenges like cybersecurity risks, connectivity issues, and update failures, which can disrupt operations if not handled properly.
Key takeaways for secure and reliable OTA updates include:
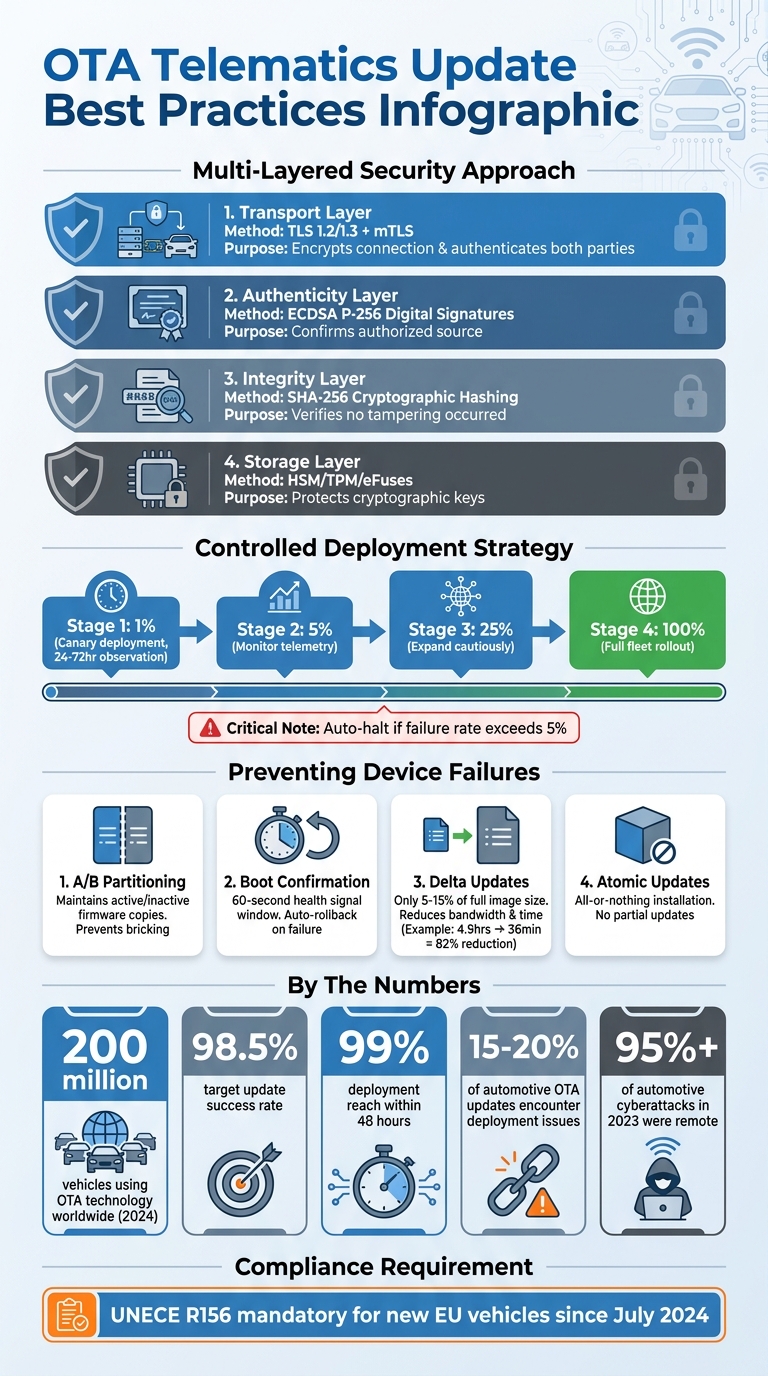
- Security: Use encryption (TLS 1.2/1.3), cryptographic hashing (e.g., SHA-256), and digital signatures to ensure updates are safe and untampered.
- Controlled Rollouts: Deploy updates in stages (e.g., 1% → 5% → 25% → 100%) to catch issues early and avoid widespread failures.
- Fail-Safes: Implement A/B partitioning to prevent bricking vehicles, and use rollback mechanisms for faulty updates.
- Connectivity Management: Use delta updates to minimise data usage and enable resumption protocols for interrupted downloads.
- Monitoring: Track update performance in real-time and conduct post-deployment checks to ensure updates work as intended.
With proper planning and execution, OTA updates can improve fleet performance, reduce costs, and ensure compliance with regulations like UNECE R156, which became mandatory in July 2024 for new vehicles in the EU.
OTA Telematics Update Security and Deployment Best Practices
Security Measures for OTA Telematics Updates
When an update leaves the server, it faces potential threats. Protecting its journey and ensuring the update arrives intact requires a layered approach to security.
Encryption and Data Integrity
Transport Layer Security (TLS) 1.2 or 1.3 forms the backbone of secure communications for OTA updates, encrypting the connection between the server and the vehicle. But with evolving threats, basic encryption isn't enough. Mutual TLS (mTLS) adds an extra layer by requiring both the server and the vehicle to authenticate with valid certificates, effectively blocking Man-in-the-Middle attacks.
Encryption during transit is just one piece of the puzzle. To ensure the update's integrity, cryptographic hashing plays a crucial role. A SHA-256 hash - a unique digital fingerprint of the firmware package - is created before the update leaves the server. Once the vehicle receives the update, it recalculates the hash. If the hashes don’t match, the vehicle immediately rejects the update, ensuring no tampering occurred during transit.
For added security, asymmetric code signing is used. Algorithms like ECDSA P-256 generate a digital signature that confirms the update comes from an authorised source. The vehicle verifies this signature against a root certificate stored securely in its Hardware Security Module (HSM) or Trusted Platform Module (TPM). These modules protect cryptographic keys, even if the operating system is compromised.
| Security Layer | Primary Method | Purpose |
|---|---|---|
| Transport | TLS 1.2+ / mTLS | Ensures confidentiality and authenticates server and client |
| Authenticity | Asymmetric Signing (ECDSA) | Confirms the update originates from an authorised source |
| Integrity | SHA-256 Hashing | Verifies the package hasn’t been altered or corrupted |
| Storage | HSM / TPM / eFuses | Protects private keys and root certificates from extraction |
Once data integrity is secured, attention shifts to controlling update initiation.
Authentication and Authorisation
Only authorised individuals or systems should initiate updates. Role-Based Access Control (RBAC) restricts access to critical systems, ensuring only approved personnel can launch updates. Adding multi-party authorisation, which requires two approvals, further reduces risks.
Each vehicle should have a unique X.509 certificate rather than a shared fleet key. This allows compromised certificates to be revoked individually using a Certificate Revocation List (CRL) or Online Certificate Status Protocol (OCSP), limiting the impact of a breach.
To bolster security, the Uptane framework is specifically designed for OTA updates in vehicles. It uses "threshold signing", requiring multiple authorised signatures, and targets specific vehicles by their VINs to ensure updates reach only the intended recipients.
Real-world examples highlight the importance of robust authentication. In mid-2024, Kia fixed a vulnerability in its owner portal that allowed unauthorised remote vehicle control using just a licence plate and VIN. Similarly, in 2018, BMW collaborated with researchers to address 14 vulnerabilities that could have allowed malicious code injection during OTA updates.
Rollback Prevention and Incident Response
Preventing rollback attacks is another key element. These attacks attempt to install older firmware versions with known vulnerabilities. Monotonic version counters, stored in non-volatile hardware like e-fuses, prevent this by only allowing firmware with higher version numbers to be installed.
Incident response is equally critical. Real-time telemetry monitoring can detect unusual behaviour, such as unexpected reboots, and trigger automated halts or rollbacks to minimise damage.
A/B partitioning provides an additional safeguard. Updates are installed on an inactive partition, leaving the current firmware untouched. The system only switches to the new partition after verifying its integrity and successful boot tests. If the new firmware fails, the vehicle reverts to the previous version automatically.
Other precautions include maintaining an emergency offline recovery key, securely stored in an HSM, to sign and deploy recovery images if the primary signing system is compromised. Linking a Software Bill of Materials (SBOM) to signed updates enhances traceability, allowing quick identification of affected vehicles when a new vulnerability is discovered. Under UNECE Regulation No. 156 (R156), which became mandatory for new vehicles in the EU in July 2024, this level of traceability is not just recommended - it’s required.
At GRS Fleet Telematics, we’ve built our OTA update infrastructure with these principles in mind, ensuring every connected vehicle remains secure.
sbb-itb-499a7f0
Deployment Strategies for OTA Updates
Once security measures are handled, the next challenge is ensuring updates reach devices smoothly. A poorly executed rollout can overload systems or, worse, leave devices unusable. Gradual and controlled strategies are key to scaling deployments while keeping systems intact.
Staged Rollouts and Canary Deployments
Rolling out an update to the entire fleet in one go is a risky move. Instead, staged rollouts deploy updates incrementally, often following a sequence like 1% → 5% → 25% → 100%. This phased approach lets teams assess real-world performance before extending the rollout further.
The process starts with a canary deployment, targeting a small group - typically 0.5% to 1% of vehicles. This subset serves as an early warning system, flagging issues like memory leaks, hardware mismatches, or problems with unstable cellular connections. Before moving to production, engineering teams should ensure at least 100 successful test updates across different hardware configurations.
"A staged rollout with observability is often the only way to prevent a 1% failure from becoming a 100% catastrophe." - Memfault
Between each stage, observation periods of 24 to 72 hours allow teams to analyse telemetry data for anomalies. If failure rates exceed 5%, automated mechanisms should pause or stop the rollout immediately. A notable example occurred in January 2026 when RND Square pushed a firmware update to 8,000 connected sensors without a staged rollout. The result? A 30% failure rate, costing approximately £163,200 in recovery expenses due to manual site visits at £68 per device.
AI-driven systems add another layer of control, monitoring factors like battery health, firmware behaviour, and unusual traffic patterns. These systems can automatically trigger updates - or rollbacks - based on the data they collect. With these strategies in place, robust fail-safe measures act as a final safety net during the update process.
A/B Partitioning and Fail-Safe Mechanisms
A/B partitioning splits the device's memory into two sections: active and inactive. The system only switches to the new firmware after confirming its integrity. If the updated firmware fails to boot or crashes repeatedly, the bootloader reverts to the previous version, ensuring the device remains operational.
One critical safeguard is the boot confirmation window. Here’s how it works: the new firmware must send a "healthy" signal within a set timeframe - usually 60 seconds or after a few boot cycles. If no signal is received, the system automatically rolls back to the earlier version. This mechanism was instrumental in avoiding widespread failures during the RND Square incident. After implementing A/B partitioning with a 60-second boot confirmation, their devices handled power outages and poor connectivity without issue.
Another essential practice is atomic updates. These ensure that updates are fully installed or not installed at all, avoiding partially updated systems that could leave devices unusable. As QuarkAndCode states:
"Every over‑the‑air (OTA) update is surgery on a live device. Do it well, and you add features, fix bugs, and harden security without anyone touching a screwdriver. Do it poorly and you risk bricking hardware".
| Mechanism | Function | Reliability Benefit |
|---|---|---|
| A/B Partitioning | Maintains two firmware copies (active/inactive) | Prevents bricking; device stays functional on old firmware |
| Boot Confirmation | Requires a "healthy" signal from new firmware | Automatically triggers rollback if the new version fails |
| Delta Updates | Sends only the differences (5–15% of full image size) | Reduces data costs and download time, minimising update risks |
| Staged Rollout | Incremental release (1% → 5% → 25% → 100%) | Limits potential issues to a small test group before full rollout |
Scheduling and Bandwidth Optimisation
Timing and efficiency play a huge role in successful deployments. Pushing updates during peak hours can disrupt operations, so scheduling them during maintenance windows or overnight is ideal.
To prevent backend overload, randomised polling ensures devices check for updates at staggered intervals - such as once per hour - instead of all at once. This avoids the "thundering herd" effect, where simultaneous requests overwhelm servers.
Delta updates are another key strategy. By transmitting only the differences between firmware versions (typically 5–15% of the full image size), they significantly cut down on bandwidth usage and data costs. Pre-update health checks further enhance reliability, verifying parameters like battery charge, available storage, and RAM before starting the update process.
At GRS Fleet Telematics, these strategies are integrated into our OTA infrastructure, ensuring updates are delivered efficiently while keeping vehicles operational and secure.
Managing Connectivity Challenges
Fleet vehicles often encounter unreliable connectivity, particularly in rural or underground areas. These interruptions can disrupt over-the-air (OTA) updates, potentially leaving devices inoperable. To address this, OTA systems must be able to handle such disruptions seamlessly. Strategies like incremental updates and robust resumption protocols are crucial for maintaining functionality.
Incremental Updates for Low Bandwidth
Delta updates, which transmit only the changes in firmware instead of the entire file, significantly reduce data usage. For instance, in November 2024, Silicon Labs tested its Delta DFU technology across 153 Bluetooth mesh nodes. A full firmware update (256,844 bytes) required 4.9 hours to complete, whereas a delta patch (19,708 bytes) took just 36 minutes – an impressive 82% reduction in deployment time. For battery-powered telematics devices, this not only cuts transmission time but also conserves energy, extending the device's operational lifespan.
Before deploying a delta update, it's essential to confirm the device's current software version and hash. After the update, generating a secure hash of the reconstructed firmware ensures it matches the approved version bit-for-bit. This process is equally important for managing intermittent connectivity, as it ensures disrupted updates can resume without starting over.
Handling Intermittent Connectivity
When vehicles move between areas with varying network coverage, connection drops can occur. To mitigate this, OTA systems should include resumption protocols that allow downloads to pick up where they left off rather than beginning anew.
Using A/B partitioning, as previously discussed, ensures that any interruptions during the download process do not impact the active firmware. Once the download is complete, file integrity is verified using SHA-256 checksums and cryptographic signatures before the update is applied atomically. This approach prevents partially updated systems from becoming unusable.
"An estimated 8.5% of the devices in a large fleet can fail within three years when supported by a poorly designed OTA update solution".
At GRS Fleet Telematics, these strategies are deeply embedded in our OTA infrastructure. This ensures that your fleet remains operational, even in areas with challenging connectivity.
Monitoring and Post-Deployment Validation
Even the best deployment strategies need continuous monitoring and validation to ensure systems remain reliable. After a secure deployment, real-time monitoring plays a crucial role in identifying and addressing issues immediately. It's worth noting that about 15–20% of automotive OTA updates encounter some form of deployment issue, ranging from partial failures to rollbacks. Without proper oversight, even a minor problem in a small test group can escalate into a fleet-wide disaster.
Real-Time Monitoring and Reporting
For effective monitoring, your system needs to track every stage of the update process: from notification receipt to download initiation and completion, pre-installation validation, installation progress, post-installation validation, and final activation. This level of detail ensures you can pinpoint exactly where issues arise - whether it's a network problem during the download or insufficient storage disrupting installation.
Context-aware telemetry is key to turning failure alerts into actionable insights. Your monitoring system should capture data on vehicle conditions such as battery voltage, ignition status, available storage, and ambient temperature. This information helps differentiate between actual software issues and environmental factors. For example, a failed update might be caused by low battery levels rather than a corrupted software package.
Advanced platforms also use automated circuit breakers to halt rollouts if failure rates exceed specific thresholds. These thresholds should be tailored to the component's criticality: 1–2% for critical systems, 3–5% for powertrain, and 5–10% for infotainment.
Once real-time metrics indicate a successful installation, post-deployment checks confirm that the update performs as expected.
Post-Deployment Health Checks
Building on the insights from real-time monitoring, post-deployment health checks ensure that the update is functioning correctly. Key metrics to monitor include crash-free sessions, watchdog timer resets, memory usage, and boot success rates immediately after deployment. Industry benchmarks typically aim for update success rates of at least 98.5% across targeted devices, with deployment reach goals of 99% within 48 hours.
Security integrity checks are another critical step. These verify that each ECU (Electronic Control Unit) is running the authenticated firmware version. Devices must validate the installed image against the signed manifest. Remote attestation using measured boot logs adds an extra layer of security, ensuring no unauthorised rollbacks to older, vulnerable versions occur and maintaining a consistent security posture across all vehicles.
At GRS Fleet Telematics, these robust monitoring and validation measures are integral to our white-label OTA infrastructure, ensuring your fleet stays secure and operational after every update.
Conclusion
This guide has outlined key security measures and deployment strategies for managing OTA updates effectively. Ensuring secure OTA updates demands a multi-layered approach and careful planning. The core principles are straightforward: implement critical security measures like hardware-backed roots-of-trust and A/B partitioning, and release updates in staged phases to identify and resolve issues before they impact an entire fleet. As the Uraeus Engineering Team warns:
"A compromised update pipeline can deliver malicious firmware to every vehicle in a fleet simultaneously, making OTA security a top-priority concern for automotive cybersecurity engineering."
The financial and operational stakes are evident. For instance, in July 2021, Porsche had to recall 43,000 Taycan and Taycan Cross electric vehicles due to software issues causing power loss. This scenario, which incurred significant costs, could have been avoided through remote OTA updates in compliance with UNECE Regulation No. 156. With this regulation becoming mandatory for all new vehicles starting in July 2024, adhering to these standards is no longer optional but a legal necessity in today's automotive industry.
Fleet managers should prioritise differential updates to reduce bandwidth consumption while leveraging Software Bills of Materials (SBOMs) to track and address vulnerabilities. These practices not only prevent major failures but also extend the lifespan of vehicles, lower warranty expenses, and open doors for subscription-based feature enhancements.
The connected vehicle ecosystem is growing at an unprecedented pace. By 2024, approximately 200 million vehicles worldwide were utilising OTA technology - a number projected to double by 2030. Moreover, over 95% of automotive cyberattacks in 2023 were carried out remotely. These trends emphasise the critical need for secure and scalable OTA strategies, particularly for fleets in the UK, to stay ahead of both compliance requirements and cybersecurity threats.
At GRS Fleet Telematics, we integrate these best practices into our solutions to ensure your fleet remains secure, compliant, and efficient. By adopting these strategies, you can safeguard your vehicles against evolving risks and set your fleet up for long-term success.
FAQs
How can we prevent a vehicle from being bricked during an OTA update?
Updating a vehicle's software over-the-air (OTA) can be tricky, but there are ways to minimise risks and prevent serious issues like "bricking" the vehicle. Here’s how:
- Staged rollouts: Start by testing updates on a small group of vehicles before deploying them to the entire fleet. This helps identify potential issues early.
- Automated rollback: Make sure there’s a system in place to revert to the previous stable firmware if something goes wrong during the update.
- Cryptographic verification: Always verify the firmware using cryptographic methods to confirm its authenticity and integrity before installation.
- Telemetry gating: Use real-time monitoring to track the update process and quickly detect any problems as they arise.
These steps help create a safer, more dependable process for OTA updates, reducing the chances of costly errors.
What should we do if an OTA update is interrupted by poor signal?
When an OTA update gets interrupted due to a poor signal, it's crucial to have a fault-tolerant and recoverable process in place. To achieve this, focus on these key practices:
- Verify update integrity: Always confirm the update files are complete and uncorrupted before applying them.
- Maintain a firmware backup: Keep a copy of the current firmware to ensure the system can revert if something goes wrong.
- Implement rollback or recovery options: Design the system to either resume the update or safely return to its previous state without losing functionality.
These steps minimise risks, ensuring the system remains stable and functional even during unexpected interruptions.
How can we prove our OTA process meets UNECE R156 requirements?
To align with UNECE R156 compliance, your Over-The-Air (OTA) update process should prioritise robust security measures. This includes employing encryption, authentication protocols, and secure key management to protect updates from tampering or unauthorised access.
Additionally, maintain thorough documentation of all procedures. This should cover aspects like version control, update verification, and rollback mechanisms to ensure transparency and reliability in your process.
For a more formal demonstration of compliance, you might consider seeking an independent audit or acquiring a certification. This can provide external validation that your procedures meet the regulation's standards.




